favorites unscripted
Let's get textual

HAPPY READING
May 29
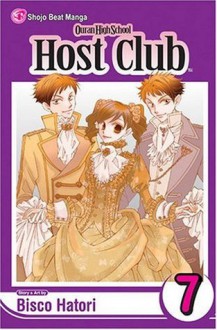
Hunny's little brother, Chika, pays a visit to the Host Club--and immediately starts attacking Hunny, using all his martial-arts prowess against his older brother! Chika seems to be the absolute opposite of his sweets-loving, Bun-Bun-toting sibling, but why is he so angry with Hunny? The Host Club is determined to find out the cause...
Review: I really enjoyed this volume . First the gang brought Koyo to the mall when he was half asleep then he ran into Haruhi stopped a seller from selling counterfeit art .Then Tamaki calls security for Koyo as a lost child.We meet Mori and Hunny brothers . Chika thinks Hunny is a alien cause he's always eating cake at night and Hunny and Chika fight and Hunny stills wins .Haruhi gets kidnapped by the all girls school the host club and Haruhi dad go to girls school to see what's going on . The play is going on and Haruhi isn't very good at singing and the girls found out the host club came to the school. The last part is a short story about the twins when they were kids their Nanny was planning on robbing the twins and she does they give her the code . Their mom asks the twins if they gave her the code so they cried they faked the tears .


Presley is a party planner (I mean event coordinator!) who also has ADHD. She was laid off at her prior job in the psych department at the U of San Fran. She has a habit of diagnosing people. Her mom, who now has dementia, was a successful party planner, so Presley hopes to take up the reins. She gets a chance hosting the mayor's surprise wedding....at Alcatraz. Things don't go as planned and there are 2 dead bodies and Presley is considered a suspect.
I did like this. I was interested and the who-done-it was good, as was the motivations behind it. But, Presley came off as a ditz. Did I mention she has ADHD & she taught psych? Sometimes when a character says something stupid/wrong/pick your poison, it makes them more relate-able. Not so much with Presley. The secondary characters were fun.
Will I read the next and rest in series? Nah. (And did you know Presley was a psych major..... and has ADHD? The reminders constantly got old. Fast.)
I read this for Romance-opoly Sleuth Street moon track
SQL Injection is The most widespread stability vulnerabilities online. Here I’ll consider to elucidate in detail this type of vulnerabilities with examples of bugs in PHP and possible answers.
If You're not so confident with programming languages and web technologies you may well be thinking what SQL remain for. Properly, it’s an acronym for Structured Question Language (pronounced “sequel”). It’s “de facto” the conventional language to entry and manipulate info in databases.
Currently most Internet sites depend upon a database (ordinarily MySQL) to keep and access info.
Our example will probably be a common login kind. Web surfers see Those people login varieties daily, you place your username and password in after which the server checks the qualifications you equipped. Okay, that’s straightforward, but what comes about just on the server when he checks your credentials?
The consumer (or user) sends towards the server two strings, the username and the password.
Ordinarily the server will likely have a database by using a table wherever the user’s facts are stored. This table has no less than two columns, just one to retailer the username and one particular with the password. Once the server gets the username and password strings he will query the databases to see In the event the supplied qualifications are valid. He will use an SQL statement for that which will appear to be this:
Pick out * FROM customers Exactly where username=’SUPPLIED_USER’ AND password=’SUPPLIED_PASS’
For those of you who are not knowledgeable about the SQL language, in SQL the ‘ character is utilised like a delimiter for string variables. Below we utilize it to delimit the username and password strings supplied Force HTTP to HTTP through the consumer.
In this example we see which the username and password equipped are inserted in the question in between the ‘ and all the question is then executed from the database motor. When the question returns any rows, then the provided qualifications are valid (that consumer exists from the database and has the password which was provided).
Now, what comes about if a consumer sorts a ‘ character in to the username or password area? Nicely, by putting only a ‘ to the username industry and residing the password discipline blank, the query would grow to be:
Find * FROM customers In which username=”’ AND password=”
This would set off an error, Because the databases engine would evaluate the end of your string at the second ‘ and then it would result in a parsing mistake in the 3rd ‘ character. Permit’s now what would transpire if we would send this enter data:
Username: ‘ OR ‘a’=’a
Password: ‘ OR ‘a’=’a
The query would develop into
SELECT * FROM buyers Where by username=” OR ‘a’=’a’ AND password=” OR ‘a’=’a’
Due to the fact a is always equal to a, this query will return all of the rows in the table buyers along with the server will “think” we equipped him with valid qualifications and let as in – the SQL injection was effective :).
Now we are going to see some extra advanced strategies.. My example will likely be based upon a PHP and MySQL System. In my MySQL databases I designed the following desk:
CREATE Desk end users (
username VARCHAR(128),
password VARCHAR(128),
e-mail VARCHAR(128))
There’s a single row in that table with data:
username: testuser
password: tests
electronic mail: testuser@tests.com
To examine the qualifications I designed the subsequent query in the PHP code:
$query=”find username, password from buyers in which username='”.$consumer.”‘ and password='”.$go.”‘”;
The server can also be configured to print out faults triggered by MySQL (this is beneficial for debugging, but need to be averted over a manufacturing server).
So, previous time I confirmed you ways SQL injection fundamentally is effective. Now I’ll explain to you how can we make more advanced queries and the way to use the MySQL mistake messages to acquire a lot more information about the database structure.
Allows start! So, if we set just an ‘ character from the username area we get an mistake concept like
You may have an error within your SQL syntax; Examine the handbook that corresponds for your MySQL server Model for the correct syntax to implement close to ”” and password=”’ at line one
That’s since the question turned
pick username, password from buyers exactly where username=”’ and password=”
What happens now if we try and set into your username industry a string like ‘ or person=’abc ?
The query becomes
decide on username, password from users wherever username=” or consumer=’abc ‘ and password=”
And this give us the mistake information
Mysterious column ‘consumer’ in ‘exactly where clause’
That’s great! Making use of these mistake messages we are able to guess the columns while in the table. We could endeavor to put from the username subject ‘ or e mail=’ and since we get no error message, we recognize that the e-mail column exists in that desk. If We all know the e-mail handle of the user, we will now just try with ‘ or email=’testuser@tests.com in both equally the username and password fields and our query turns into
find username, password from buyers exactly where username=” or electronic mail=’testuser@screening.com’ and password=” or e-mail=’testuser@screening.com’
and that is a valid question and if that email handle exists from the table we will correctly login!
You can even use the mistake messages to guess the table name. Due to the fact in SQL You should utilize the table.column notation, you'll be able to make an effort to put within the username area ‘ or consumer.exam=’ and you will see an mistake information like
Mysterious table ‘user’ in where by clause
High-quality! Allow’s check out with ‘ or end users.test=’ and We've got
Not known column ‘people.check’ in ‘where clause’
so logically there’s a table named customers :).
Fundamentally, In the event the server is configured to present out the error messages, You should utilize them to enumerate the database framework and Then you certainly may be able to use these informations in an attack.