Obecnie wykształciły się trzy-cztery typy urządzeń z ekranem wykonanym w technologii papieru elektronicznego - pierwsza grupa to „tradycyjne” czytniki, zaprojektowane do możliwie komfortowej lektury e-booków (większość produktów marki Kindle, Kobo, PocketBook, Tolino). Drugą grupę stanowią wyspecjalizowane notatniki służące głównie do prowadzenia odręcznych notatek, gdzie czytanie e-booków może być dość poboczną funkcją (reMarkable, Supernote). Trzecia jest połączeniem czytników i notatników, gdzie funkcje notowania nie są bardzo rozbudowane i są raczej dodatkiem do pracy z e-bookami (Kindle Scribe, Kobo Elipsa 2E).

PocketBook InkPad Eo z kolorowym ekranem i rysikiem do odręcznych notatek
No i czwarta to tablety pracujące pod Androidem, umożliwiające instalację większości aplikacji mobilnych, często obudowane wieloma funkcjami (jak obsługa rysika, rozpoznawanie odręcznego tekstu) i służące głównie do prowadzenia odręcznych notatek. PocketBook InkPad Eo jest przykładem tej ostatniej grupy, w której rozwój najwyraźniej wierzy PocketBook, bo to już kolejne (po InkPadzie X Pro) w ciągu roku tego typu urządzenie producenta. Przez ostatni miesiąc używałem go intensywnie, zapraszam więc do lektury wyników testu. Przekonajmy się jak PocketBook radzi sobie na nowym polu.
PocketBook InkPad Eo od strony technicznej
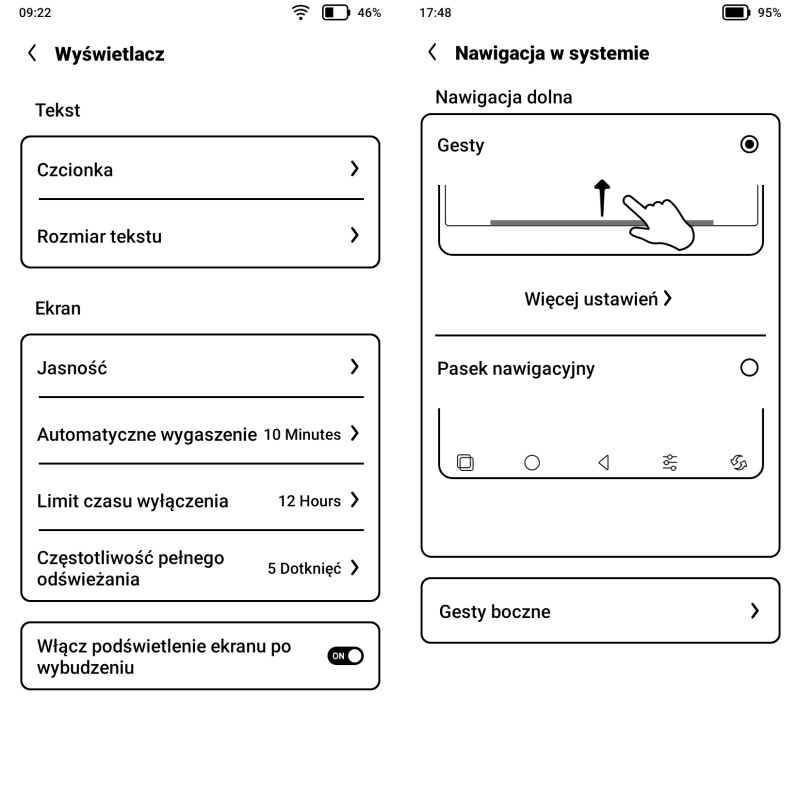
PocketBook InkPad Eo to androidowy tablet z kolorowym ekranem wykonanym w technologii papieru elektronicznego. Oznacza to przede wszystkim możliwość wygodnej pracy na nim w świetle słonecznym przy jednoczesnej bardzo dobrej widoczności obrazu. Ekran ma przekątną 10,3 cala (26,12 cm) przy wymiarach 154x206 mm (dla porównania - kartka A4 ma 210x297 mm). W przypadku treści czarno-białych wyświetla je z rozdzielczością 300 ppi (2480x1860 pikseli), a kolorowych 150 ppi (1240x930 pikseli). Trzeba mieć na uwadze, że w urządzeniach z ekranem E-Ink Kaleido 3 kolory (4096) wyświetlane są znacznie mniej intensywnie niż w nowoczesnych ekranach jakie znamy ze smartfonów czy tabletów. Podobnie jest w przypadku recenzowanego urządzenia. Ekran posiada wbudowane oświetlenie, które umożliwi korzystanie w trudnych warunkach oświetleniowych ale i przyda się na co dzień. A to dlatego, że ekran E-Ink Kaleido 3 ma mniejszy kontrast od podobnych ekranów czarno-białych i do komfortowego czytania (szczególnie treści kolorowych) trzeba z niego często korzystać przy oświetleniu włączonym na poziomie 50-60% natężenia. Oświetlenie rozprowadzane jest całkiem równomierne, choć przy szerszej krawędzi ramki otaczającej ekran można się dopatrzeć lekkiego cienia. Jakość światła można dopasować do własnych upodobań przy pomocy regulacji temperatury barwowej.

Największym atutem InkPada Eo jest kolorowy ekran o przekątnej dziesięciu cali
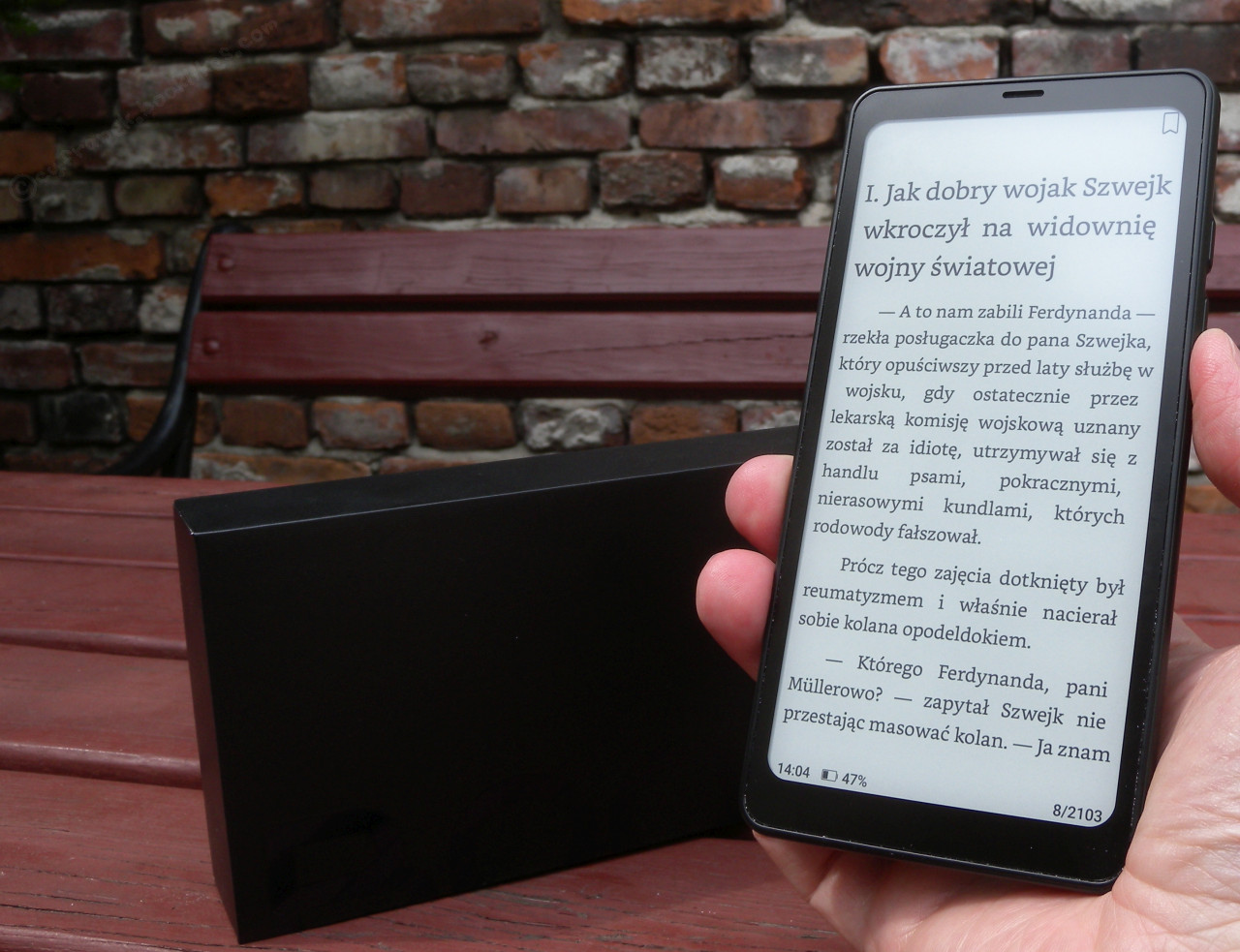
PocketBook InkPad Eo wyposażono w ośmiordzeniowy procesor 2,3 GHz i 4 GB pamięci operacyjnej. W większości przypadków wystarcza do całkiem płynnej pracy aplikacji mobilnych, które można pobierać z dostępnego w urządzeniu Google Play Store. Zainstalowany w czytniku Android 11 powinien jeszcze przez przynajmniej kilka lat umożliwiać wgrywanie nowszych wersji programów. Z racji rozmiarów ekranu InkPad Eo nie należy do małych, mierzy 226х191х7 mm i waży 470 g (położony bez ryska na mojej wadze kuchennej ma 461 g). Na pliki użytkownika jest ok. 51,3 GB pamięci wewnętrznej (64 GB pomniejszone o system operacyjny). Jeśli to za mało, można skorzystać z gniazda kart microSD. W stronę wielofunkcyjnego tabletu przesuwa go też wyposażenie w aparat fotograficzny (na pleckach), głośniki (stereo) i mikrofony (na krawędzi obudowy).

Na pleckach obudowy znajduje się kamera i dioda doświetlająca
Obudowa sprawia solidne wrażenie. Jest prosta, ale to tylko zaleta. Jako, że plecki są gładkie, to jedynym czego jej brakuje są gumowe nóżki, które by ograniczały ślizganie się po stole/biurku przy odręcznym pisaniu. Na obudowie jest tylko jeden fizyczny przycisk - wyłącznik. Umieszczony został na krawędzi krótszego boku obudowy. W zależności od aplikacji czy wykonywanej czynności, może to być dolna, boczna czy górna krawędź. W moim przypadku ułożenie Eo dość dynamicznie się zmienia w zależności, czy notuję, czytam czy też robię jeszcze coś innego. Niestety, wielokrotnie “w ferworze” tych działań zdarzało mi się niechcący wyłączać urządzenie, bo ów wyłącznik często jakoś znajdował się znienacka pod dłonią lub którymś palcem. Niby niewielki kłopot, bo Eo szybko się usypia i szybko wybudza, ale to jednak irytujące, gdy ciągle muszę zważać na to jak trzymam urządzenie aby go przypadkowo nie wyłączyć. Chyba najlepiej gdyby wyłącznik był w zagłębieniu na pleckach, albo na środku dłuższej z krawędzi obudowy? Tam rzadziej “przypadkowo” naciska się palcami.

Wyłącznik znajduje się na krótszej krawędzi obudowy
PocketBook InkPad Eo powstał w ramach współpracy z chińską firmą Bigme, która miała w swoim dorobku już kilka różnych urządzeń pracujących pod kontrolą Androida.

W ekranach E-Ink Kaleido 3 można dostrzec artefakty z poprzednio wyświetlanych stron (ghosting) i podobnie jest w InkPadzie Eo
Rysik
Jako, że mowa tu o tablecie przeznaczonym do notowania, szczególną uwagę należy poświęcić rysikowi. Wykonany jest on w pasywnej technologii Wacom, co oznacza, że nie trzeba go ładować ani wkładać do niego baterii. To rozwiązanie często stosowane w notatnikach. Więc jeśli z jakiegoś powodu firmowy rysik znajdujący się w zestawie nie będzie nam odpowiadał, albo go zgubimy, łatwo znaleźć zastępnik.

Rysik typy Wacom dołączony w zestawie
A więc po pierwsze - „nie będzie nam odpowiadał” trudno mi sobie wyobrazić. Miałem co prawda w ręku kilka, a nie kilkadziesiąt rysików, ale spokojnie można stwierdzić, że PocketBook dołączył bardzo miły dodatek. Z wyglądu i odczuć jest on zbliżony do uważanego za „wzorcowego” rysika Kindle Scribe Premium. W porównaniu z nim rysik dołączony do InkPada Eo jest jednak trochę grubszy i tylko część boków jest matowa (mniej śliska). Ja bym akurat wolał, gdyby był trochę cieńszy, ale ogólne wrażenie z jego używania jest bardzo pozytywne. Sądzę, że dla osób o drobnych dłoniach może być za gruby do komfortowego pisania przez dłuższy czas.

W górnej części rysika jest gumka do mazania
W górnej końcówce jest gumka do mazania, która bardzo dobrze reaguje z ekranem. No i jeszcze po drugie - „albo go zgubimy” to niestety w InkPadzie Eo jak i w rysiku zabrakło magnesów, które umożliwiałyby choćby chwilowe mocowanie go do krawędzi obudowy. Takie rozwiązanie jest bardzo często stosowane w tego typu urządzeniach, bo jak rysik jest przy notatniku/tablecie to go nie musimy szukać i też łatwiej z niego skorzystać bo jest raczej pod ręką. No i może trudniej zapodziać. Dlatego kupując etui, warto sprawdzić, czy jest w nim miejsce na umocowanie rysika. W pudełku obok rysika, są także trzy zapasowe końcówki („stalówki”).
Przesiadka z czytnika PocketBook - za i przeciw
PocketBook znany jest na naszym rynku bardzo dobrze, ale głównie z czytników książek elektronicznych pracujących pod kontrolą Linuksa. Recenzowane urządzenie ma w nazwie „InkPad”, podobnie jak obecne już wcześniej na rynku czytniki np. InkPad 4 czy InkPad Color 3. Jednak istotnie od nich się różni, ponieważ InkPad Eo jest wielofunkcyjnym tabletem pracującym pod kontrolą Androida. To trzeci androidowy produkt w ofercie producenta (po dostępnym tylko w Chinach InkPadzie Color i czarno-białym InkPadzie X Pro). Tego typu tablety i notatniki z ekranami z papieru elektronicznego znajdują się już w ofercie większości producentów czytników. Zapewne więc niejeden posiadacz czytników zastanawiał się nad przejściem na tego typu urządzenia. Zobaczmy jakie są argumenty „za i przeciw” takiej migracji?
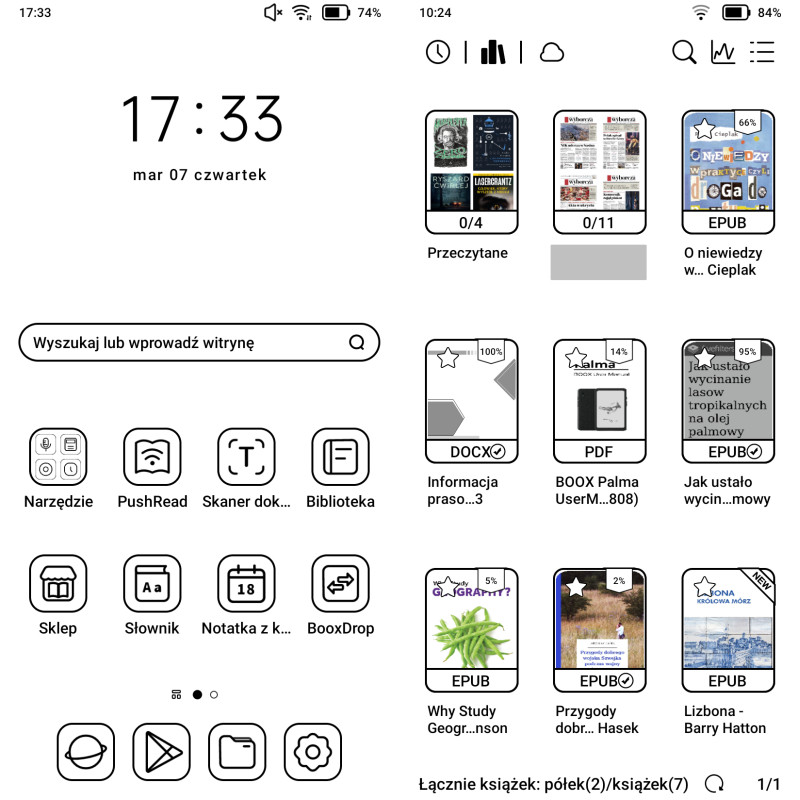
Wybierając notatnik lub tablet zwykle nie tracimy podstawowej funkcji czytnika, ponieważ wspomniane urządzenia nieźle sobie radzą z plikami PDF (zależnie od wybranej aplikacji, jakości ekranu i wydajności sprzętu). Co prawda w domyśle PDF-y mają być bazą do notatek, ale aby coś notować, to trzeba wcześniej wczytać czy też przeczytać. Podobnie jest z e-bookami w formacie EPUB. Tu także są aplikacje dostarczone przez producenta jak i możliwość korzystania z ulubionej aplikacji mobilnej.
Tablety (jak Eo) obok funkcji odręcznego notowania dają też możliwość instalacji wielu różnorodnych aplikacji. Funkcjonalność tego typu urządzeń jest więc zwykle znacznie większa niż w przypadku typowego czytnika. Czy oznacza to odejście czytników do lamusa? Niekoniecznie, bo specjalistyczne urządzenia skupione na jednej funkcji mają się wciąż nieźle.

PocketBook InkPad Eo ma bardzo uproszczone zarządzanie księgozbiorem (ekran po lewej), a wczytywanie książek do niego może być zadziwiająco skomplikowane (ekran po prawej) w porównaniu z czytnikami e-booków tej marki
Spójrzmy teraz na argumenty przemawiające przeciw przesiadce. Przede wszystkim przy rezygnacji z czytnika tracimy prostotę i całą ergonomię wypracowaną po to aby się skupić na czytaniu. Czytnik włączamy i już możemy czytać. W tablecie nic nie jest tak proste i oczywiste. Weźmy na przykład usługę Send-to-PocketBook, która pozwala wysyłać na czytniki własne dokumenty czy zakupy z polskich księgarń. W recenzowanym tablecie mi tego bardzo brakuje. Nie mogę w prosty (i automatyczny) sposób skierować na tablet ani zakupów, ani prenumeraty prasy ani artykułów pobranych ze stron WWW. To znaczy jakoś tam mogę, ale każda z tych czynności wymaga znacznie więcej mojego czasu i uwagi. Czyli w sumie marnuję czas na coś co w czytniku książek jest oczywiste i wygodne. Jak to wygląda w przypadku prenumeraty “Gazety Wyborczej”? Na czytniku otrzymuję codziennie nowe wydanie po skonfigurowaniu (jednorazowym) usługi Send-to-PocketBook i ustawieniu (jednorazowym) w Publio automagicznej wysyłki kolejnych wydań na adres czytnika. Zaś na Eo musiałem zainstalować osobną aplikację Dropbox, co wiązało się z usunięciem dwóch wcześniej podpiętych do tego dysku chmurowego urządzeń (nie płacę abonamentu za dostęp do Dropboksa, więc mogę teraz mieć tylko trzy urządzenia). Następnie w Publio (jednorazowo) przełączyłem wysyłkę prenumeraty z Send-to-PocketBook na Dropbox. I teraz za każdym razem (czyli codziennie) aby przeczytać nowe wydanie “Wyborczej” muszę uruchomić aplikację Dropbox, wejść w odpowiedni katalog i pobrać ostatnie wydanie. I jeszcze je skasować w chmurze, żebym następnego dnia nie pobrał go ponownie bez potrzeby. No i na koniec ręcznie zaimportować pobrany plik aby był widoczny w aplikacji Biblioteka (jeśli dla porządku go pobrałem do podkatalogu BooksWyborcza na przykład). Niby nie tak znowu wiele wysiłku, ale jak się człowiek przyzwyczaił do tego, że najnowsze wydanie gazety już czeka na czytniku, gdy się go rano włącza, to jednak denerwuje. Mam nadzieję, że PocketBook weźmie przykład np. z inkBooków, gdzie analogiczna do Send-to-PocketBook usługa działa w najnowszych czytnikach tej marki (także pracujących pod Androidem).

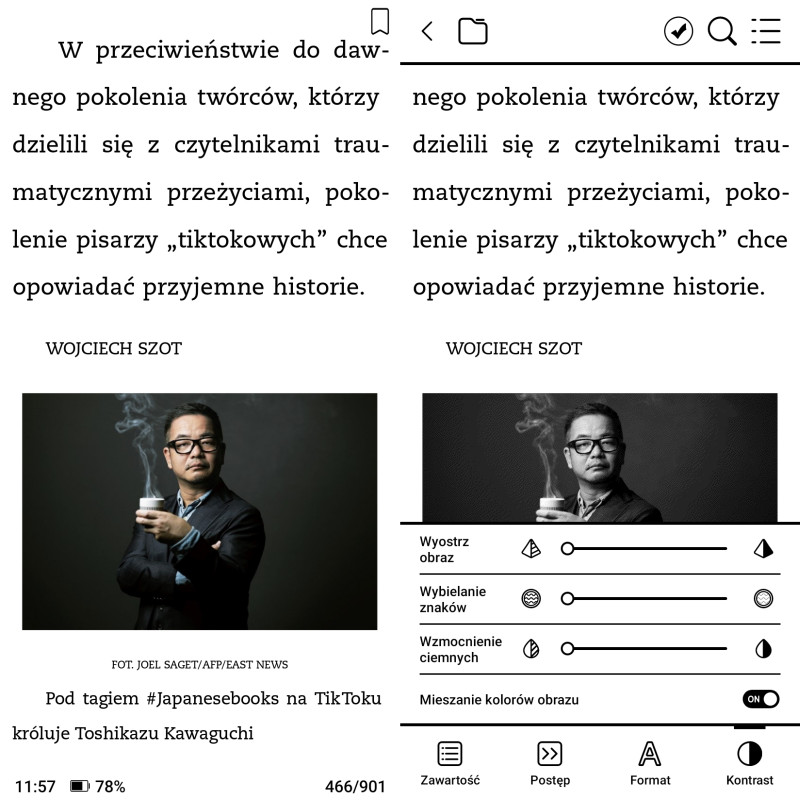
PocketBook InkPad Eo - mobilna aplikacja Legimi działa sprawnie
Trochę podobna sytuacja jest z polskimi wypożyczalniami - Legimi i Empik Go, które na czytnikach PocketBook doczekały się własnych aplikacji. Ich największą zaletą jest to, że pobrane w ramach abonamentu książki (tylko e-booki, czytnikowe aplikacje nie obsługują audiobooków) trafiają do czytnikowej biblioteczki i są traktowane jak każdy inny e-book wgrany do czytnika. Można w nich m.in. używać słowników, własnych czcionek i dodawać notatki. W przypadku Eo można zainstalować aplikacje mobilne zarówno Legimi i Empik Go jak i innych wypożyczalni, choćby Boobeat, Storytel czy Audioteki. Mamy więc większy wybór usługodawców oraz dostęp nie tylko do e-booków ale i audiobooków. Tracimy zaś sporo z komfortu lektury, ponieważ aplikacje mobilne wypożyczalni mają zwykle tylko bardzo podstawowe opcje związane z wyglądem tekstu, a o słownikach czy własnej czcionce tym bardziej można zapomnieć. Trzeba też pamiętać, która książka skąd pochodzi, bo jest dostępna tylko w rodzimej aplikacji. Można przywyknąć ale jak dla mnie do komfortu daleko.

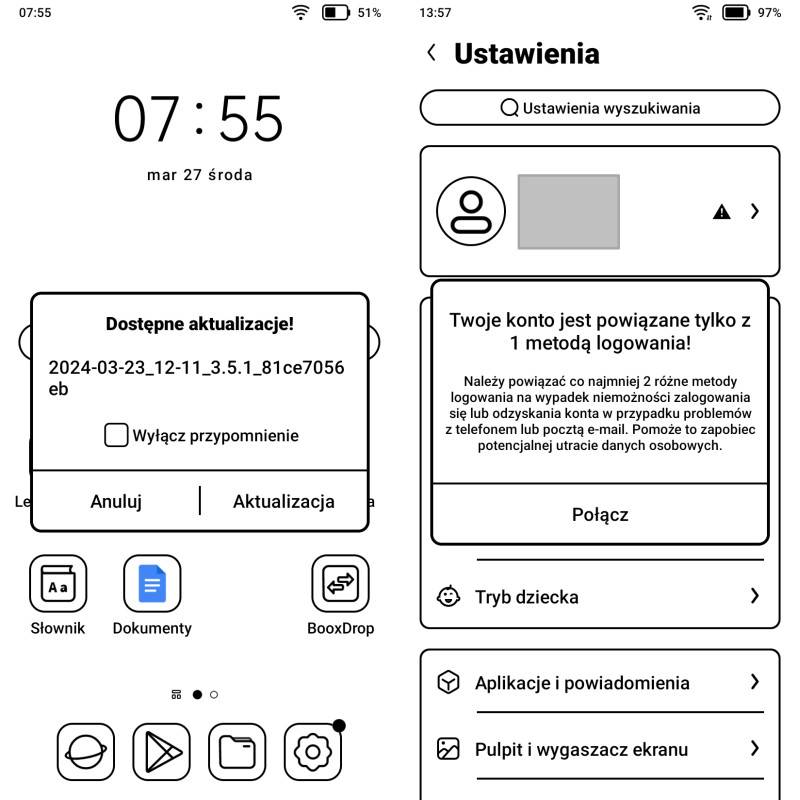
PocketBook InkPad Eo ma spore możliwości zmiany wyglądu menu (ekran po lewej) jak i kontroli ustawień systemowych (ekran po prawej)
Nie bez znaczenia jest też oczywiście cena. Dobry czytnik, choć z mniejszym ekranem, można kupić o połowę taniej niż InkPad Eo. Jeśli jednak potrzebujemy funkcjonalności oferowanej przez androidowy tablet z ekranem E-Ink i rysikiem, to będzie wartość dodana, która kosztuje.

Zainstalowane domyślnie aplikacje mają dopasowaną szatę graficzną ikon (ekran po lewej), zaś tryb pracy aplikacji (i jakość obrazu) w dodanych przez użytkownika warto kontrolować pod kątem sposobu wyświetlania treści na ekranie poprzez "centrum papieru elektronicznego" (ekran po prawej)
Nie piszę tego aby zniechęcać do korzystania z Eo czy innych podobnych urządzeń. Bo wspomniane „zalety” i „wady” nie dotyczą tylko recenzowanego tabletu. Po prostu trzeba mieć świadomość, że tablety i czytniki to różne urządzenia i niestety pozostaje dylemat - coś za coś. W przypadku tabletów jesteśmy pozostawieni z „otwartym” Androidem i jego możliwościami ale pozbawieni wypracowanej latami na czytnikach ergonomii korzystania w postaci całościowego podejścia producenta i skupienia na książce. W przypadku wyboru tabletu mamy znacznie większe możliwości, które sprawdzą się głównie przy pracy z tekstem. Chyba, że PocketBook wpadnie na przykład na pomysł hybrydy, gdzie będzie opcja przełączania Eo w „tryb czytnika” gdzie będziemy „zaopiekowani” tak samo jak podczas korzystania z typowego czytnika właśnie. Wtedy dylemat czytnik/tablet zniknie…
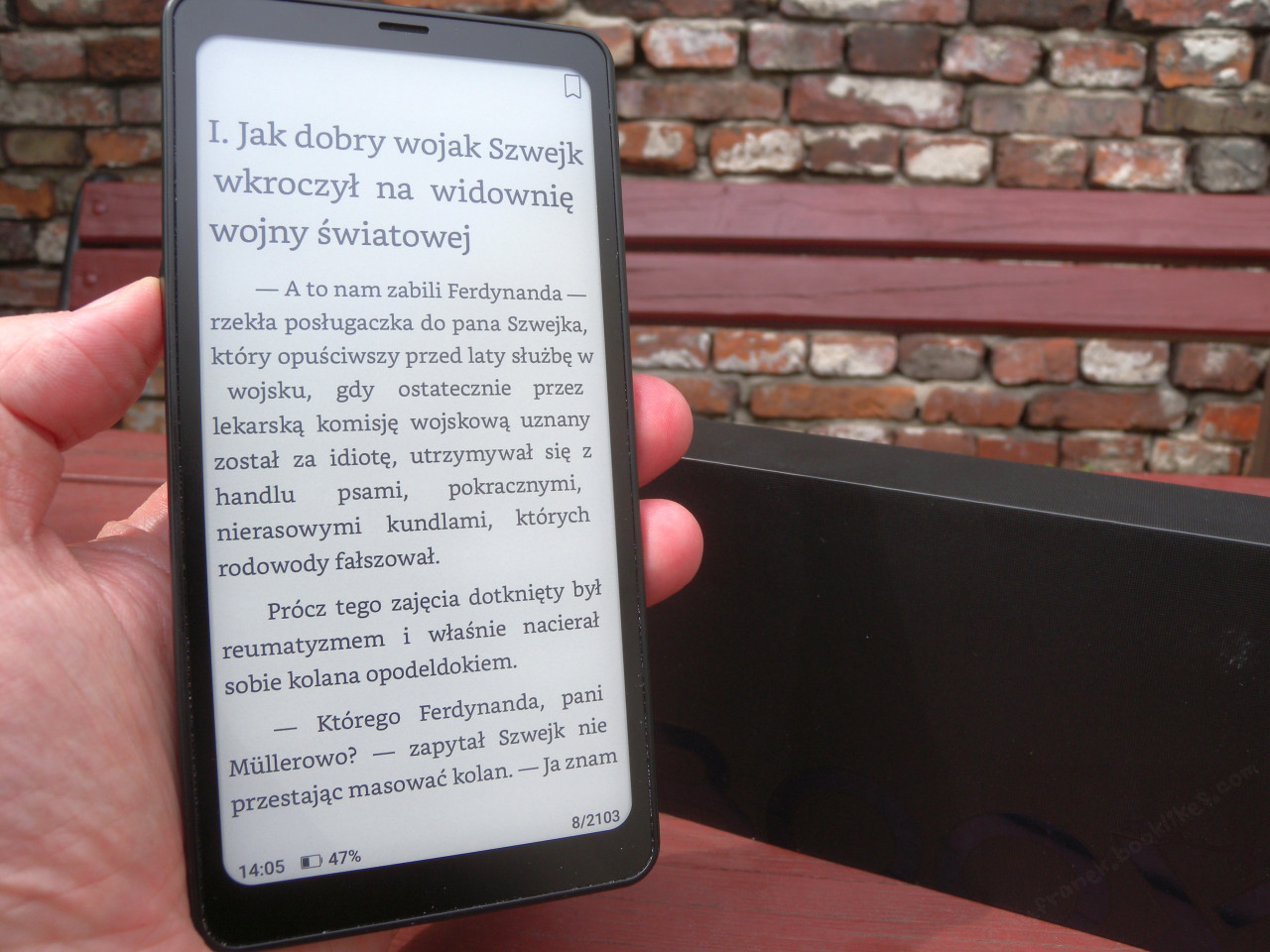
PocketBook InkPad Eo jako czytnik - xReader czy PocketBook Reader?
Książki do InkPada Eo można wgrywać na przykład przy pomocy kabla USB C, najlepiej od razu do katalogu Books. Można też do tego używać bezpłatnego programu Calibre. Nie mamy tu do dyspozycji wspomnianej wcześniej usługi bezprzewodowej wysyłki na adres e-mail urządzenia (Send-to-PocketBook). Można też e-booki wgrać przez lokalną sieć, skanując kod QR generowany na InkPadzie i otwierając odpowiednią stronę np. na smartfonie czy komputerze. Sama biblioteczka ma dość podstawowe możliwości, szczególnie z wzorcowym rozwiązaniem na czytnikach PocketBook. Książki widać jako listę lub okładki. Grupowane mogą być w katalogach zapisanych w pamięci urządzenia.

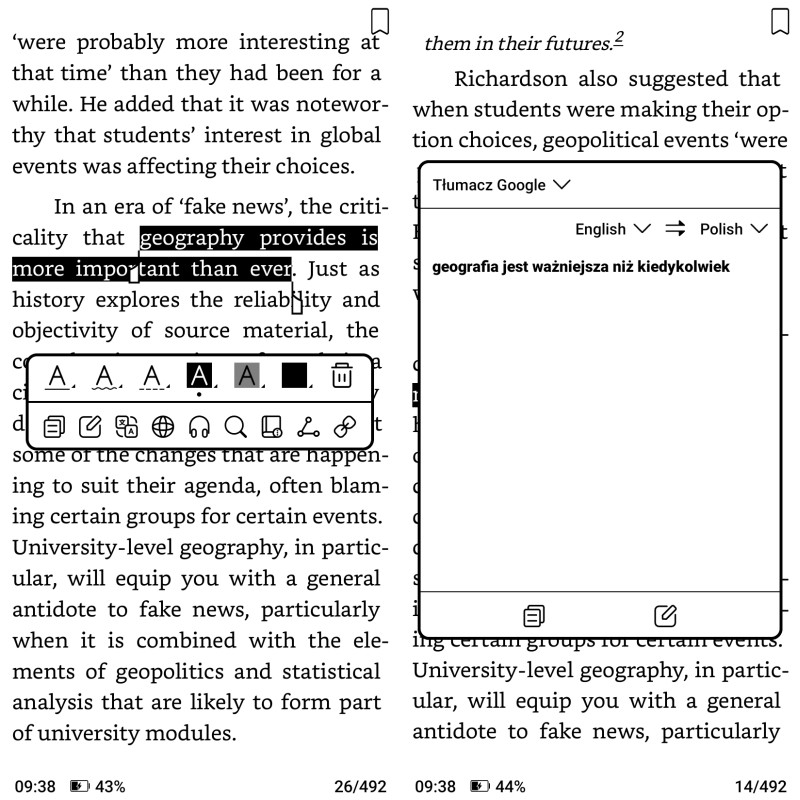
Mocną stroną PocketBook Readera jest możliwość dodania Tłumacza Google (ekran po lewej) i chmury PocketBook Cloud (ekran po prawej)
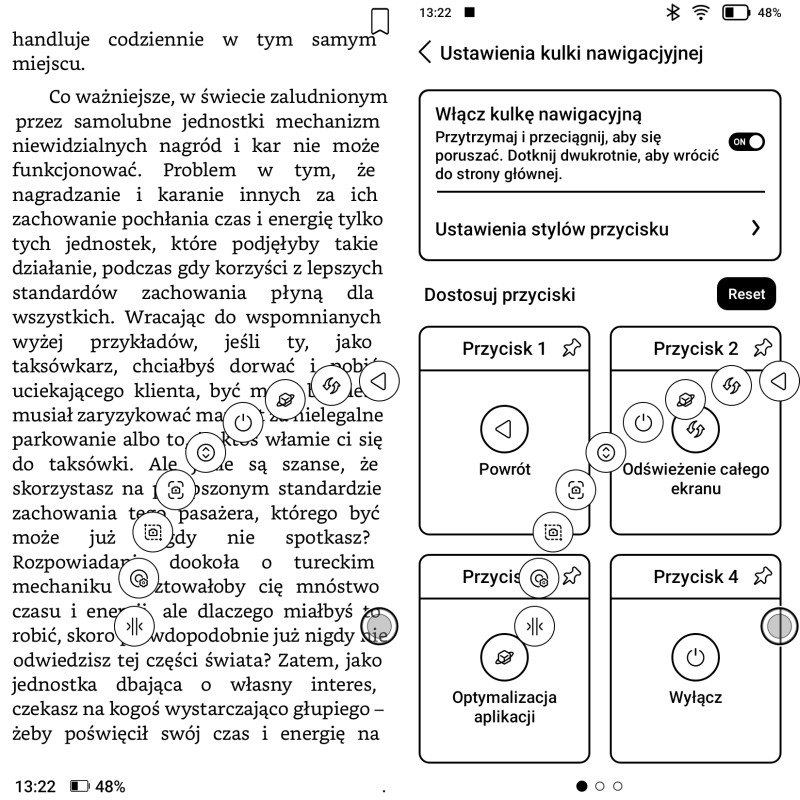
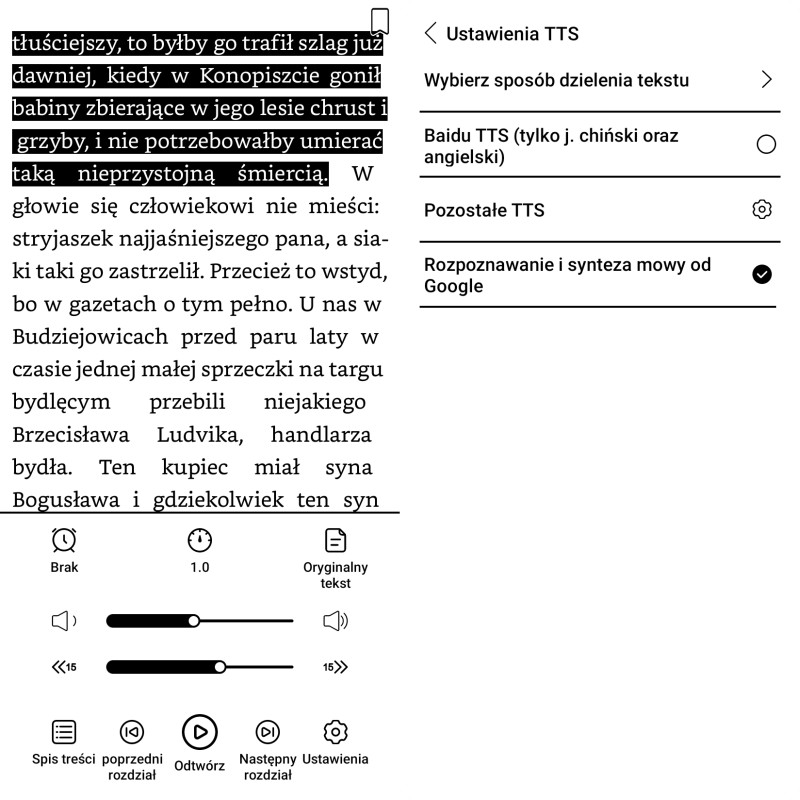
W InkPadzie Eo znajdziemy dwie domyślnie zainstalowane aplikacje służące w zasadzie do tego samego: wyświetlania plików (PDF, EPUB itp.) i ewentualnie dokonywania w nich notatek czy zakreśleń. Trudno mi powiedzieć, dlaczego tak się stało, ale wprowadza to niepotrzebny bałagan. Jednak z każdą chwilą przekonuję się, że PocketBook Reader byłby zbędny, gdyby nie jego dwie cechy - możliwość współpracy z Tłumaczem Google i dostęp do dysku chmurowego PocketBook Cloud. W każdym innym aspekcie xReader jest lepszy i stabilniejszy w działaniu. Choć w sumie PocketBook Reader ma jeszcze jedną funkcję, której brak w xReaderze. To odczytywanie tekstu przez mechanicznego lektora (TTS). No ale za każdym razem jak próbuję tę opcję uruchomić w PocketBook Readerze, to się wywala.

W PocketBook Readerze nie udało mi się przetestować opcji mechanicznego lektora (TTS), ponieważ aplikacja przestawała działać przy każdej próbie (ekran po lewej), a i przy wyświetlaniu tekstu bywają kłopoty z wyborem własnej czcionki (ekran po prawej) bo program nie zawsze uwzględnia wybrany krój
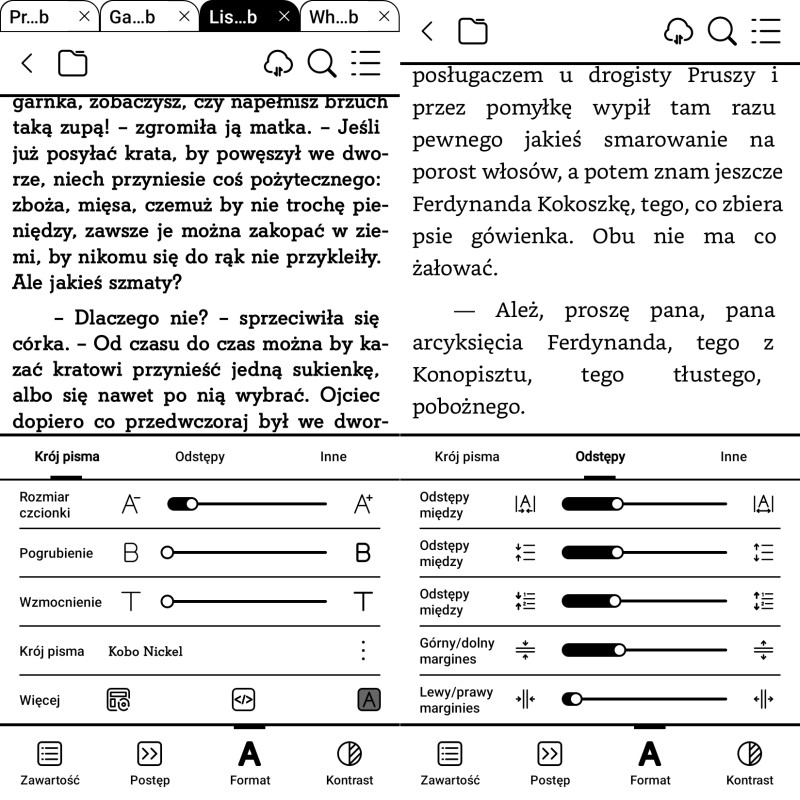
Żadna ze wspomnianych aplikacji nie jest w pełni funkcjonalna i zadowalająca. W obydwu brakuje też na przykład ładnych czcionek, jest za to masa bezużytecznych krojów, przez które trzeba się przedzierać aby znaleźć coś sensownego. Ale na szczęście można dodać własne czcionki. W przypadku xReadera pliki należy wgrać do katalogu xreader/fonts, zaś dla PocketBook Readera do katalogu fonts. Przy okazji można skasować trochę krojów gruzińskich czy hebrajskich jeśli nie będą nam potrzebne.

Zainstalowany w InkPadzie Eo xReader umożliwia dodawanie odręcznych notatek także w kolorach (ekran po lewej), jednak zaznaczanie tekstu możliwe jest tylko na szaro (ekran po prawej)
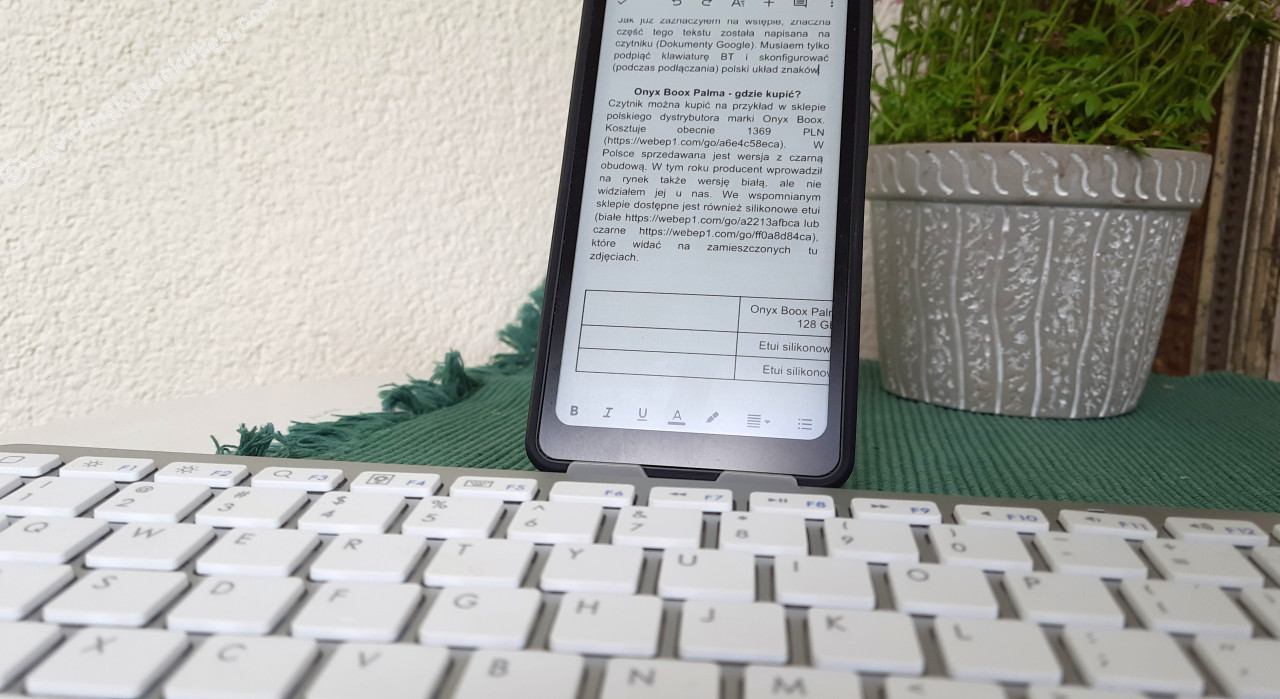
Ostatecznie do codziennego czytania przerzuciłem się na KOReadera, choć wcale tego nie planowałem. Aplikacja ta działa stabilnie i czyta się w niej wygodnie. Jest w niej nawet dostęp do Tłumacza Google.
Odręczne notatki
Notowanie przy pomocy rysika to jedna z głównych funkcji InkPada Eo. Świadczy o tym domyślne umieszczenie aplikacji „Przydatne notatki” na górze paska ikon zawierającego najczęściej używane aplikacje. Notatki są zintegrowane częściowo z kalendarzem, bo pojawiają się tam w dniu ich wykonania i z kalendarza można je też wywołać. Tu warto zwrócić uwagę, że tydzień w aplikacji kalendarzowej zaczyna się w niedzielę, a nie w poniedziałek, co u nas może być mylące. W każdym razie mi się ciągle myli. Ja domyślnie tydzień w kalendarzu „widzę”, że zaczyna się od poniedziałku, nawet jeśli tak nie jest w danej aplikacji. A potem się dziwię, dlaczego notatka wpisana na środę (domyślnie trzeci dzień od lewej, czyli od początku tygodnia) jest w czytnikowej aplikacji kalendarza widoczna we wtorek (faktycznie trzeci od lewej, bo pierwsza tu wyświetlana jest niedziela).

Przydatna funkcja InkPada Eo to odręczne notatki, które można także robić na wielostronicowych plikach z aktywnymi odsyłaczami, jak na przykład kalendarze
W programie do tworzenia notatek mamy cztery niezbyt się różniące narzędzia do pisania/rysowania: pióro, ołówek, pędzel i długopis. Każde posiada po pięć grubości kreski i możliwość wybrania jednego z dwunastu kolorów. Moim zdaniem zróżnicowanie grubości kreski jest zbyt małe. Bez względu na to, czy rysik trzymamy pod mniejszym czy większym kątem, kreska na ekranie jest takiej samej grubości.

W notatkach do dyspozycji mamy dwanaście kolorów i pięć grubości kresek rysika
Notatki można grupować w tworzone przez użytkownika kolekcje. Do pisania po ekranie trzeba się przyzwyczaić. Powierzchnia ekranu w InkPadzie Eo jest dość śliska, więc pisze się jak na papierze kredowym. Tworzenie notatek uprzyjemnia zestaw gotowych szablonów tła (kartka w linie, kratkę itp.) oraz możliwość dodawania warstw. Szczególnie ta druga opcja jest wygodna, bo możemy tworzyć fragmenty strony, które można modyfikować bez obawy ingerencji w treści z sąsiedniej warstwy.

W aplikacji do notatek jest także opcja dodawania prostych figur geometrycznych
Podczas tworzenia odręcznych notatek mamy także do dyspozycji dodatkowe narzędzia:
- lasso (na górnej belce) - pozwalające uchwycić i przeciągnąć w inne miejsce fragment notatki;
- strzałkę (na górnej belce) - pozwalającą wysłać notatkę w postaci pliku graficznego;
- rozpoznawanie tekstu (na górnej belce) - pozwalające zmieniać pismo odręczne na maszynowe (także w języku polskim);
- obrazek (na bocznym pasku) - pozwalające dodać grafikę znajdującą się w pamięci urządzenia;
- tekst (na bocznym pasku) - pozwalające dodać tekst maszynowy (bez wyboru czcionki ale z możliwością formatowania, na przykład pogrubienia);
- kształty (na bocznym pasku) - pozwalające dodać linie, strzałki czy figury geometryczne;
tła (na bocznym pasku) - pozwalające zmienić tło;
- nowa strona (na bocznym pasku) - dodające kolejną stronę do notatki.

Aplikacja do odręcznych notatek posiada spory zbiór teł do wyboru (ekran po prawej), a same notatki można dzielić na warstwy (ekran po lewej)
Osobną grupą notatek są zapiski na plikach PDF (artykuły, organizery). Popularne są zwłaszcza kalendarze z podziałem na każdy dzień i rodzaj aktywności. Tego typu pliki korzystają z mnóstwa wewnętrznych odsyłaczy, aby na przykład z widoku miesiąca (szybko) przejść do konkretnego dnia w roku. Dla xReadera zainstalowanego w InkPadzie może to być wyzwanie, bo takie dokumenty liczą sobie po kilkaset stron. Zdarzało mi się w takich przypadkach dłuższą chwilę oglądać klepsydrę wyświetlaną na ekranie w oczekiwaniu na przeskok do odpowiedniego miejsca. Co ciekawe, pomagało często wywołanie pełnego odświeżenia ekranu. W xReaderze zdziwił mnie trochę brak możliwości zakreślania tekstu różnymi kolorami w plikach PDF. Da się wybrać kolor zakreślacza z menu, ale korzystając z narzędzia aplikacji do zaznaczania, tekst tak czy inaczej będzie zacieniowany na szaro. W PocketBook Readerze przy zaznaczaniu tekstu palcem do wyboru są trzy kolory. Rysikiem można tylko pisać lub rysować po tekście.

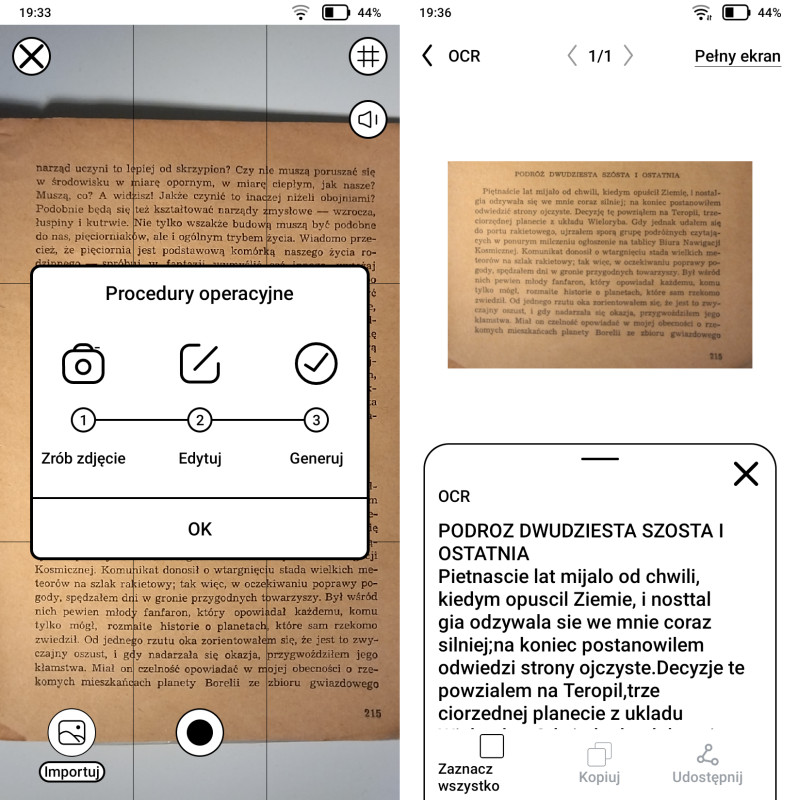
Bardzo mocną stroną aplikacji do notowania jest (ekran po lewej) sprawnie działająca opcja rozpoznawania pisma odręcznego (OCR), zaś dzielenie się notatkami możliwe jest przez pocztę elektroniczną (ekran po prawej)
Bardzo ważnym atutem InkPada Eo jest dla mnie opcja rozpoznawania pisma odręcznego. Delikatnie to ujmując nie piszę zbyt wyraźnie (a słowo „ładnie” nawet mi w tym zdaniu nie przeszło przez klawiaturę). Tymczasem czytnik bardzo dobrze radzi sobie z przerabianiem moich zwyczajnych bazgrołów na pismo maszynowe. Nie wiem, jaki mechanizm zastosowano, ale działa. Podejrzewałem nawet, że zrzuty ekranu wysłane są do jakiegoś ChataGPT (tak jest w Bigme), ale chyba nie, bo czytnik odłączony od internetu też poprawnie rozpoznaje moje pismo. To o tyle ważna funkcja, że w InkPadzie Eo nie ma tekstowego przeszukiwania odręcznych notatek. Zamiana na pismo maszynowe może ułatwić późniejszą pracę z tekstem. Notatki oraz ich wersję tekstową można szybko udostępnić wysyłając na wskazany przez użytkownika adres poczty elektronicznej.
PocketBook InkPad Eo - gdzie kupić?
InkPada Eo można kupić m.in. w firmowym sklepie polskiego dystrybutora marki. Kosztuje obecnie 2379 PLN. W polskim Amazonie InkPada Eo wyceniono na 2199 PLN. Ceny warto sprawdzać i porównać przez zakupem urządzenia, bo zmieniają się dość dynamicznie.

PocketBook InkPad Eo w sklepie polskiego dystrybutora marki (źródło: czytio.pl)

PocketBook InkPad Eo w polskim oddziale Amazonu (źródło: amazon.pl)
Dostępna jest także firmowa okładka w kolorze czarnym, która kosztuje 189 PLN. Prezentuje się bardzo solidnie, jest dobrze dopasowana do InkPada Eo i przyjemna w dotyku. Wydaje się dobrze spełniać funkcję ochronną.

Firmowa okładka prezentuje się bardzo solidnie

Firmowa okładka mocowana jest na magnesach do plecków InkPada Eo
Jeśli szukamy czegoś lżejszego czy tańszego, ale też (niestety) znacznie delikatniejszego, można poszukać uniwersalnego etui, które będzie przeznaczone też na podobnej wielkości urządzenia innych marek. Podczas testowania InkPada Eo jako tako sprawdziło mi się niedrogie etui przeznaczone także np. na Kindle Scribe czy Kobo Elipsę 2E. W środku ma gumkę na umocowanie rysika, a klapka przytrzymywana jest dwoma niewielkimi magnesikami. Można je kupić na Aliekspressie w cenie ok. 9 USD, dostępne jest w kolorze beżowym, szarym i błękitnym.

Sprawdziło mi się niedrogie uniwersalne etui, które ma miejsce na umocowanie rysika i pasuje także na inne tego typu urządzenia
Podsumowanie
PocketBook InkPad Eo to urządzenie przeznaczone dla osób lubiących odręczne notowanie i przeznaczone głównie do pracy. Sprawdza się nie tylko przy odręcznym notowaniu ale i szeroko pojętych działaniach z tekstem. Swoje atuty pokaże głównie przy świetle dziennym i w ruchu. Ja na przykład bardzo polubiłem InkPada, gdy chodząc po halach i między halami Targów IFA w Berlinie, na szybko notowałem sobie rysikiem, co i gdzie. No i właśnie na recenzowanym tablecie powstawały ostatnie teksty, które publikowałem na blogu. Korzystałem przy tym głównie z Dokumentów Google. InkPad Eo znacznie mniej sprawdził mi się jako czytnik, ponieważ żadna aplikacja nie zapewniała mi na nim takiego komfortu jak „zwykły” czytnik książek. Chociaż jak już sobie zainstalowałem KOReadera, to obraz uległ trochę zmianie na plus.

PocketBook InkPad Eo (widoczne gniazdo USB C i kart microSD)
Warto podkreślić, że z każdą kolejną aktualizacją oprogramowania, widać postęp. Od momentu rynkowej premiery były przynajmniej dwie aktualizacje. Widać, że producentowi zależy na tym produkcie. Obecnie Na InkPadzie Eo mam najbardziej aktualny firmware 1.3.1. Być może opisywane przeze mnie kłopoty nie będą obecne, gdy ten tekst będziecie czytać w przyszłości. To dopiero drugi tablet wypuszczony na rynek przez PocketBooka, więc i nas i producenta zapewne czeka jeszcze wiele zmian i poprawek. Ale to już w tym momencie całkiem funkcjonalne i użyteczne urządzenie. Myśląc o tego typu tablecie, warto pamiętać, że na rynku lada chwila będzie dostępny też PocketBook Color Note (więcej we wpisie: „Zapowiedź: PocketBook Color Note - kolorowy notatnik z „nietłukącym” ekranem”).
Porada konsumencka na dziś brzmi: jeśli potrzebujecie czegoś z dużym ekranem do czytania, InkPad Eo nie zapewni takiego komfortu jak czytnik. Jeśli jednak ma on służyć do pracy z tekstem, warto w niego zainwestować bo do tego się nadaje.
Plusy
- porządny rysik w zestawie;
- duży ekran;
- gniazdo kart microSD;
- możliwość instalacji nawet najnowszych wersji aplikacji mobilnych (sklep Google Play);
- regulacja temperatury barwowej oświetlenia;
- polskojęzyczne menu;
- duża poprawność przetwarzania pisma odręcznego (po polsku) na maszynowe;
Minusy
- brak możliwości ustawienia poniedziałku jako początku tygodnia w systemowym kalendarzu;
- niewygodna lokalizacja wyłącznika;
- długi czas reakcji akcelerometru na obrócenie urządzenia;
- brak gumowych nóżek na pleckach obudowy;
- niestabilna firmowa aplikacja do czytania e-booków (PocketBook Reader);
- brak możliwości korzystania z tłumaczeń (Tłumacz Google) w xReaderze;
- brak możliwości zaznaczania tekstu w kolorze w xReaderze;
- sporadyczne błędy w tłumaczeniu menu i PocketBook Readera;
- brak integracji usługi typu Send-to-PocketBook;
Dane techniczne PocketBook InkPad Eo (PB 1042) wg producenta:
Ekran: przekątna 26,2 cm (10,3 cala), kolorowy dotykowy (palec lub rysik) ekran E-Ink Kaleido 3 z wbudowanym oświetleniem o regulowanej temperaturze barwowej i rozdzielczością 300 ppi (2480x1860 pikseli) dla obrazów czarno-białych i 150 ppi (1240x930 pikseli) dla kolorowych (4096 kolorów);
Masa: 470 g;
Rozmiary: 191×226×7 mm
Pamięć: ok. 51,3 GB wewnętrznej (64 GB pomniejszone o pliki systemu operacyjnego);
Obsługiwane formaty tekstowe: AZW, AZW3, DOC, DOCX, EPUB, FB2, FB2.ZIP, HTM, HTML, MOBI, PDF, PRC, RTF, TXT;
Obsługiwane formaty graficzne: PNG, BMP, JPEG;
Obsługiwane formaty dźwiękowe: MP3, WAV;
Audio: głośniki stereo, BT lub przez przejściówkę USB C-minijack;
Łączność: Wi-Fi, BT, USB C (OTG);
Procesor: 2,3 GHz (ośmiordzeniowy);
Pamięć RAM: 4 GB;
System: Android OS 11;
Bateria: 4000 mAh;
Kamera: tak;
Mikrofony: tak;
Główne funkcje: Google Play Store;
Oficjalna strona produktu: https://pocketbook.pl/pl-pl/catalog/notatki-elektroniczne/pocketbook-inkpad-eo-pl


 Log in with Facebook
Log in with Facebook